The Next Generation of Flipper Zero SAM Boards from Didgitalpunk and Red Team Tools
Many of you remember the NARD SAM boards we used to carry. Many of you also won't stop asking when they're coming back. The answer: they're not. They've been replaced by something better.
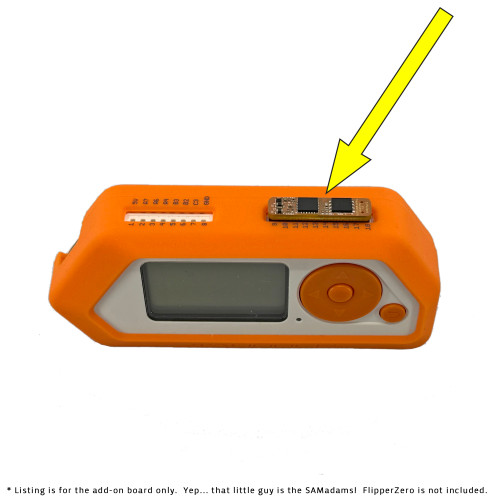
The SAMadams is a brand new Flipper Zero add-on that is functionally identical to the old NARD SAM but redesigned from the ground up. It's significantly smaller, far more robust, and the HID Secure Access Module is now soldered directly to the board. No more pocket snags, no more hunting for loose SIM-card-style SAMs, and no more sourcing a separate HID SAM on your own.
Red Team Tools is the only official source for the SAMadams. The board was designed in direct collaboration with , and we are the exclusive authorized seller. If you're buying it somewhere else, it isn't this.
What It Does
A Secure Access Module (SAM) is a secure element that stores sensitive cryptographic key material in hardware, reducing the risk of compromise. This is the same type of module found in a wide variety of third-party HID-compatible encoders, card printers, and readers.
The HID SAM on this board allows your Flipper Zero to read credential technologies that use standard keysets and SIOs, including:
-
Seos
-
iCLASS SE
-
DESFire
-
UHF
These are the same SAM boards and HID secure elements used in .
The required open-source Seader app can be found at https://lab.flipper.net/apps/seader.
NOTE: UHF processing of SIO data is supported by the SAM, but the SAMadams does not have a UHF reader. For that functionality, please see the updated FlipperMeister.
Frequently Asked Questions
Q: Does this break Seos?
No. Everything is working as designed. The SAM handles authentication challenge/response and SIO decryption entirely on-chip. This is no different than any vendor's wall reader processing a protected credential and outputting Wiegand data. The SAMadams simply lets your Flipper Zero do that same job as a battery-powered, portable reader that also happens to do a bunch of other stuff.
Q: So why would I want it?
Probably the same reason you have a Flipper Zero in the first place: convenience. If the Flipper is your hacker Swiss Army Knife, this adds another tool to it.
Q: Can I write my own Seos credentials?
No. The SAM provided here is the same type and configuration found in any normal off-the-shelf reader. It does not have encoding APIs. This is read-only.
Q: Can I copy Seos cards?
Sort of. You can't encode Seos or iCLASS SE credentials directly, but in most cases you can execute a downgrade attack: read the PACS Wiegand payload and write it back to another supported credential such as HID Prox or iCLASS.
Q: What is a downgrade attack?
Downgrade attacks have been technically possible for decades but are only recently becoming more widely understood. Check out for an introduction, or look into RTA's training for hands-on practice.
Important Notes
-
This is an add-on for the Flipper Zero. The Flipper Zero itself is not included.
-
Additional support for this item's specific capabilities is not available without special arrangement. Contact for training and hardware usage guidance if you are unfamiliar with HID secure elements.
-
Designed by
1 Review Hide Reviews Show Reviews
-
HID ✅
sick of forgetting HID work badge. Now I am the owner of a back up thanks to this!